March 25, 2026
The Rise of AI in Cybercrime: What You Need to Know
Submitted by Tier 3 I.T. Solutions
AI-driven cyberattacks are no longer a distant threat—they’re happening now, faster and harder to detect than ever. For many businesses, especially small to medium-sized ones, the risk isn’t if but when their defenses will be tested. These threats can drain your finances, shake customer trust, and disrupt operations. In this post, you’ll learn how cybercriminals use AI to outsmart traditional protections and how you can safeguard your business with the right IT services.
The New Threat Landscape
How AI Changes Cybercrime
The cybersecurity world has changed dramatically with artificial intelligence entering the picture. What once required expert hackers now becomes accessible to almost anyone with the right tools. This shift creates serious challenges for businesses of all sizes.
Sophisticated Attacks That Look Genuine
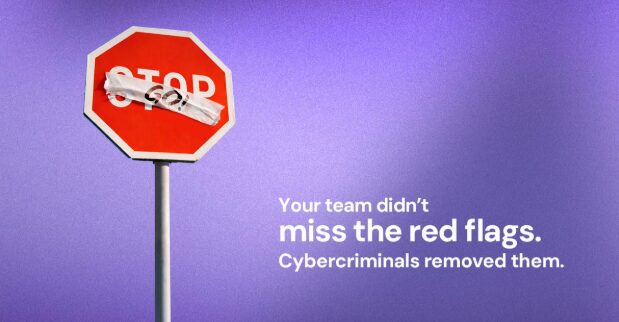
Gone are the days when phishing attempts were easy to spot through poor grammar or strange email addresses. AI now crafts perfect messages that match your company’s tone, branding, and communication style.
These messages can:
- Perfectly mimic your CEO’s writing style
- Include correct company logos and formatting
- Reference real projects or clients from public information
- Create convincing website clones that capture login credentials
Voice and Video Deepfakes
One of the most alarming trends in cyber security is the rise of deepfake technology. These AI-generated voices and videos can:
- Create calls that sound exactly like your executives
- Request urgent wire transfers or sensitive information
- Bypass voice recognition security systems
- Appear completely authentic to even careful employees
Accessible Ransomware-as-a-Service
The barrier to entry for cybercrime has fallen dramatically. Now:
- Non-technical criminals can rent AI-powered attack tools
- Attacks can be launched at scale against multiple targets
- Ransomware can adapt to avoid detection
- Small businesses face the same sophisticated threats as large corporations
Why Small and Medium Businesses Are Prime Targets
Proactive Protection: Safeguarding Your Business
Taking a proactive approach to cyber security is no longer optional – it’s essential for long-term success. Here’s how businesses can protect themselves:
Secure AI Implementation
If your business uses AI tools, proper security protocols must be in place:
- Thorough vetting of all AI platforms before integration
- Clear policies on what data can be processed through AI
- Regular security audits of AI implementations
- Proper access controls for all AI systems
- Continuous Monitoring and Response
Effective protection requires constant vigilance:
- 24/7 threat monitoring to catch attacks early
- Automated response systems for known threats
- Regular security assessments and penetration testing
- Rapid incident response when issues arise
Employee Training and Awareness
Your team is both your greatest vulnerability and your strongest defense:
- Regular cyber security courses for all staff members
- Simulated phishing and social engineering tests
- Clear protocols for verifying unusual requests
- A culture that rewards security awareness
Safeguard Your Business Before It’s Too Late
Don’t wait for an attack to improve your security posture. The time to act is now.
Book a meeting today to take the first step toward comprehensive protection for your business. Build a security strategy that protects your assets, your reputation, and your future.
Author: Since 1990, Tier 3 IT Solutions has helped businesses make the most of their technology investments. With a long-term perspective, they partner with companies to build efficiency, streamline operations, and reduce downtime. Guided by a belief in Passion, Process, and People, they focus on building systems that work — and on truly listening to the businesses they serve. Connect with Tier 3 I.T. today.
Member Blog
Want to share your story? Are you an expert in your area? Submit your blog today!
Please note: submission does not guarantee your blog will be posted.
